
One Operator. One Screen. Every Domain.
The airframe-agnostic command-and-control software layer for unmanned systems.
CRYPTIC CODEX: NEXUS / LUCY HIVEOS
Where Operator Intent Meets Kinetic Action
Nexus / Lucy HiveOS is the cryptographically-anchored command-and-control software layer that turns any Blue-UAS-cleared airframe into a swarm-coordinated, ledger-audited, mission-ready Nexus asset.
We don't sell drones. We make somebody else's drones smarter.
The Challenge: Why Defense C2 Software Falls Behind
Traditional C2 systems fail to deliver:
- Operator readiness in under 40 hours of classroom instruction
- Cognitive bandwidth when one operator manages six or more vehicles simultaneously
- Forensic audit trails that survive the loss of the central coordinator
- Cryptographically signed proof that an action was authorized - by whom - and what occurred
- Airframe and inference flexibility (most systems lock the program office to a single vendor stack)
The result: small talent pools, slow operations under pressure, and audit trails that depend on the integrity of the system that wrote them.
The Solution: Nexus / Lucy Hive OS
One operator. One screen. Every domain.
Nexus / Lucy HiveOS reduces multi-vehicle command-and-control to its essentials. Air vehicles, ground robots, surface vessels, and sub-surface platforms register in the same fleet model, track through the same data channels, and command through the same interface.
Every operator command is cryptographically signed. Every node-executed action is hash-chained into a tamper-evident ledger. Every deployed node verifies the chain independently every fifteen minutes, byte-identical to the hive.
Production today. Not PowerPoint.
Lucy-node: The Integration Primitive
Drop our ~50 MB Rust binary onto the airframe. We do the rest.
Lucy-node is the integration contract with any Blue-UAS-cleared platform. Bring us specs, a device driver, and a connection method. We install lucy-node and the platform becomes a Nexus-controlled asset within a working integration window.
- Single-file Rust binary, ~50 MB. musl + rustls. No glibc dependency.
- Drops onto Linux, macOS, or Windows. No fleet manager needed.
- Polls the hive task queue every 3 seconds. Claims work. Executes. Reports.
- Replicates the immutable ledger every 2.5 minutes. Verifies the chain every 15.
- Signed self-updates with rollback. Atomic swap. Heartbeat verification post-boot.
- Survives DDIL & continues local execution of the cached mission when the hive is unreachable.
The Nexus Operator Workstation

Twenty-five years of real-time strategy games already trained millions of operators.
We didn't invent a new interaction model. We adopted the one that already works.
Nexus is a Tauri-packaged React/TypeScript native application running on the operator's Windows, macOS, or Linux machine. CesiumJS 3D globe at 60fps. Live fleet telemetry. Hardware-bound, YubiKey-gated, two-factor kill-switch.
- Drag-select to group. Right-click to send. Shift + right-click to queue. Ctrl+1 to bind a squad.
- C for formation picker. L for line. W for wedge. C for circle. P for perimeter.
- A gamer is mission-ready in minutes, not weeks.
The talent pool is no longer constrained by who has eighty hours of classroom time available.
The Hive Coordinator
Single-process. SQLite-authoritative. RHEL with SELinux enforcing.
The Hive runs as a FastAPI/Python service on a dedicated AIL server.
78+ REST endpoints.
- WebSocket StreamRelay for real-time channels.
- Task queue with OS-aware routing.
- Circuit-breakers.
- Prometheus metrics.
- Lucile enforcement middleware on every privileged path.
The authoritative store is SQLite - not PostgreSQL. This is a deliberate architectural decision: PostgreSQL downtime does not block ledger writes. PostgreSQL is kept as an eventually-consistent analytics cache only.
The Crown Jewel: Tamper-Evident Audit Ledger
A chain no one. Including us. Can rewrite.
Every operator command and every node-executed action is written to a SHA-256 hash-chained, SQLite-authoritative, per-node-replicated immutable ledger.
- Block hashes are byte-identical across the Python and Rust implementations. CI golden-vector tests turn cross-language drift into a build failure rather than a silent audit-corruption mode.
- Every admitted node holds a full local replica. Verifies the chain independently every 15 minutes.
- Loss of the coordinator does not erase authority grants, mission configurations, or safety envelopes - they are on disk at every node.
- A compromised hive cannot silently rewrite history. Divergence is detected on the next verify cycle, by every participant in the swarm.
For an evaluator, the practical consequence is direct: a post-mission forensic pivot on any single ULID correlation ID can reconstruct the full chain - operator click to kinetic result - with cryptographic certainty.
Airframe-Agnostic by Design
Drone today. UGV tomorrow. Sub the day after. Same identity envelope. Same ledger.
Bring us specs, a device driver, and a connection method. We integrate lucy-node and the platform; air, ground, surface, or sub-surface becomes a first-class Nexus asset under the same cryptographic audit trail as every other node in the swarm.
Every asset, regardless of domain, lives under one Lucile identity envelope and one operator workstation.
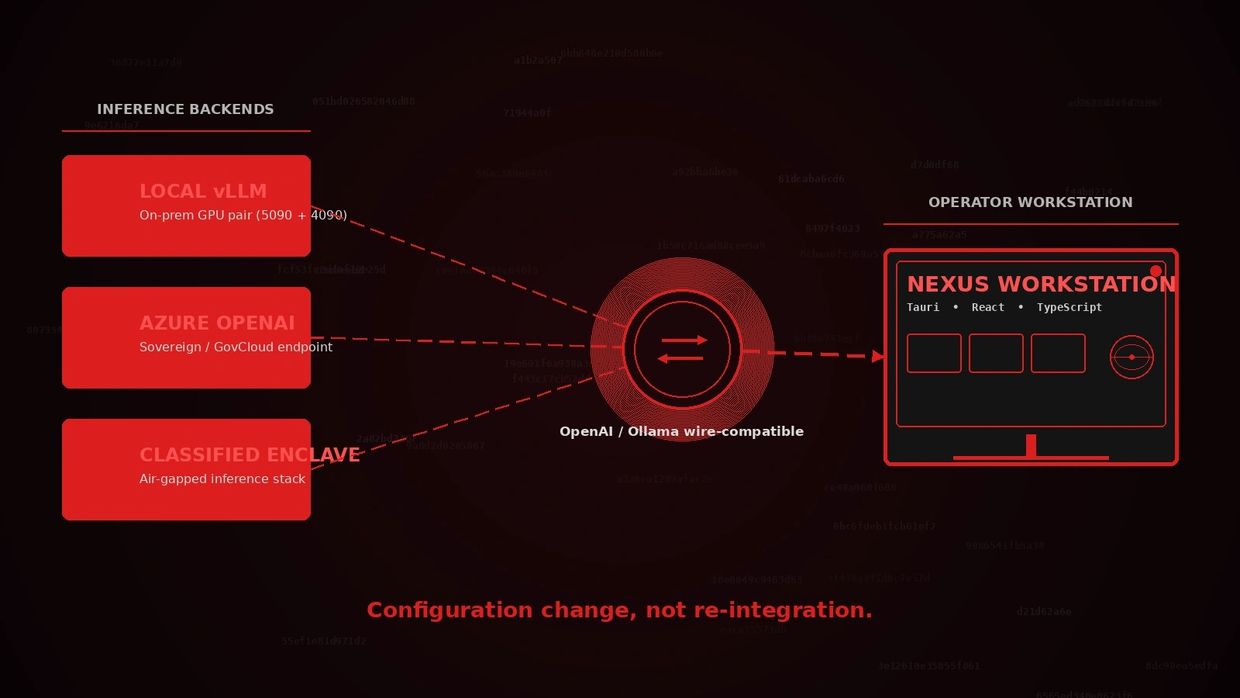
LLM-Agnostic Inference Substrate
Local vLLM today. Sovereign cloud tomorrow. Classified enclave the day after. No re-integration.
Our reasoning substrate is wire-compatible with both OpenAI and Ollama. Any client written against either standard plugs into Nexus with zero code changes.
- Hot-swap, dual-model, tensor-parallel, and smart-route orchestration modes ship today.
- Currently runs on Nvidia 5090 + 4090 with tensor parallelism enabled by default.
- Supports AWQ, GPTQ, and FP16 weights. LoRA adapters sideload for capability composition.
- Bridge to vLLM, Azure OpenAI, classified-enclave inference, or local Ollama as a configuration change - not a re-integration.
For OTA / IDIQ procurement, this is a procurement feature: the contracting authority can specify the sovereign inference stack per theater or per classification level. We don't fight that requirement. We make it a config change.
DDIL Resilience

It works when nothing else does
Byzantine-fault-tolerant peer consensus
It works when nothing else does
Military operations transpire in environments where networks fail. Nexus / Lucy HiveOS is engineered to keep working when connectivity degrades or disappears.

Four transport tiers
Byzantine-fault-tolerant peer consensus
It works when nothing else does
Bluetooth, WiFi, LoRa, LTE
Automatic dispatcher failover.
The operator never manages radios.

Byzantine-fault-tolerant peer consensus
Byzantine-fault-tolerant peer consensus
Byzantine-fault-tolerant peer consensus
When the coordinator is unreachable; Squads continue executing cached missions and coordinating among themselves indefinitely.

Local AI inference fallback
Identity rotation every 2 to 12 hours
Byzantine-fault-tolerant peer consensus
on the operator workstation. The desktop reasoning engine keeps serving when the hive is degraded.

Hardware-token authorization
Identity rotation every 2 to 12 hours
Identity rotation every 2 to 12 hours
for every kinetic-relevant command. YubiKey today; CAC and PIV adaptable.

Identity rotation every 2 to 12 hours
Identity rotation every 2 to 12 hours
Identity rotation every 2 to 12 hours
with no service interruption. A compromised key is useful for hours, not weeks.

Architecture That Scales with You
Three components. One signed transport. End-to-end identity binding.
- Operator intent at one end of the chain. Kinetic action at the other.
- Every hop Lucile-identity-bound and ledger-visible.
- One end-to-end signed transport: secured transport and C2 as a single capability, not as two components sold separately.
- Fleet management built-in: signed self-update with rollback, no separate fleet manager required.
- Identity rotation without service interruption: P-256 ECDSA keys rotate every 2–12 hours with cryptographic transition certificates.
Who We Serve
DoW Program Offices
Blue-UAS-Cleared Airframe Primes
Blue-UAS-Cleared Airframe Primes
NSTXL OTA, Drone Dominance, IDIQ vehicles, DARPA, DIU, APFIT. Need a software-layer integration counterparty for any Blue-UAS-cleared airframe? That's us.
Blue-UAS-Cleared Airframe Primes
Blue-UAS-Cleared Airframe Primes
Blue-UAS-Cleared Airframe Primes
We're open to teaming for OTA and IDIQ submissions. We bring the software layer. You bring the platform. Together: a Nexus-controlled asset under one operator and one immutable audit trail.
Allied Government Auditors
Blue-UAS-Cleared Airframe Primes
Allied Government Auditors
Cross-language hash verifiability means an allied-government auditor who only trusts their own reference implementation can still verify the chain, byte-identical to ours.
Why Choose Cryptic Codex for the C2 Layer
Three components. One signed transport. End-to-end identity binding.
- Production today, simulation-validated on real hardware: not slideware
- CMMC Level 2 self-attested with Purdue MEP support
- Cleared personnel for sensitive integration work
- Cross-language ledger verifiability: Rust + Python compute byte-identical SHA-256 hashes
- No vendor lock-in: airframe-agnostic, LLM-agnostic, cloud-agnostic
- Zero active partnerships at submission time: we name no prime, fully open for teaming
READY TO TAKE COMMAND?
Whether you're a DoW program office evaluating C2 substrates, a prime integrator looking for a software-layer teaming partner, or an OTA participant assembling a Drone Dominance response. We should talk.
This website uses cookies.
We use cookies to analyze website traffic and optimize your website experience. By accepting our use of cookies, your data will be aggregated with all other user data.